 The FAIR model (the engine powering the RiskLens cyber risk quantification platform) is a disciplined approach to cyber risk analysis that eliminates the guesswork – and the red-yellow-green color coding – from risk reporting and sets up IT risk analysts to deliver the kind of financially based analyses that the rest of the business wants to see.
The FAIR model (the engine powering the RiskLens cyber risk quantification platform) is a disciplined approach to cyber risk analysis that eliminates the guesswork – and the red-yellow-green color coding – from risk reporting and sets up IT risk analysts to deliver the kind of financially based analyses that the rest of the business wants to see.
But it does require some reprogramming for IT risk management shops – the good news is that that FAIR concepts are logical and easy to grasp (and don’t require any heavy math lifting). Here are three key skills to acquire to run an effective IT risk program based on risk quantification:
1 Scoping: Defining a Risk Scenario
Really, this is a critical thinking skill: What’s the risk question we are trying to answer and why? To answer in FAIR terms, we focus on defining a simple scenario of a loss event to analyze: A threat acting against an asset resulting in an impact. 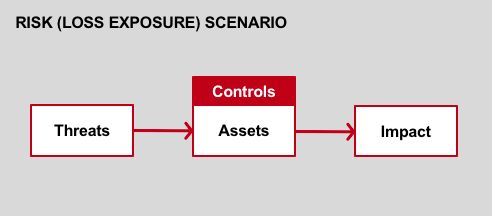 The result is a well-formed and concise statement of a risk to quantify.
The result is a well-formed and concise statement of a risk to quantify.
Example: The risk associated with a cyber criminal launching a web application attack and exfiltrating customer PII contained in the main customer database, resulting in confidentiality loss
From Case Study: Reducing Web Application Attack Risk with RiskLens
Learn More: How to Scope a Risk Analysis Using FAIR
2. Mapping Risk to the FAIR Model
To understand the FAIR model is to understand how cyber risk quantification gets done. The model is easy to grasp – you can see it on one page here as a series of buckets, with the relevant ones to be filled with data that add up at the top to the FAIR definition of risk: the probable frequency and probable magnitude of a future loss.
Filling in the buckets helps you think through the elements of frequency and magnitude; for instance, how many attempts are made against us by criminals (Threat Event Frequency) and how effective are our controls (Vulnerability)?
Learn more here: How to Map a Risk Scenario to the FAIR Model.
Good news, the RiskLens application automates the mapping process.
3. Gathering Data from SMEs Mapping the loss event scenario points the way to the task of gathering data from around your organization to put some numbers on loss event frequency and loss magnitude.
Our mantra: You have more data than you think, you need less data than you think for risk quantification.
First, know that the RiskLens application readily compensates for limited data by running mathematical simulations to calculate probabilities of loss; and the application leverages industry loss data to fill in where the organization’s own data may be lacking.
Finally, FAIR analysts can use calibrated estimation to arrive at a usefully accurate estimate when hard data is lacking (for instance, when an organization has never suffered a data breach).
That said, a key competency for risk analysis is still locating and interviewing the right subject matter experts in the organization. With your well-formed scenario and your sense of how it should map to the FAIR model, you are primed to ask the kinds of very specific questions that will elicit the most relevant answers in the least amount of time.
Example: What controls are in place to prevent a cybercriminal from getting onto database X? What percent of the time would these controls prevent a cybercriminal from getting onto database X? Use ranges to document those inputs, to capture the inevitable variance that exists in real life.
From My Game Plan for Gathering Data for Risk Analysis
Tip: Stick to filling out what's needed for the FAIR model and don’t get too far into the weeds with a SME, as there is a point of diminishing returns, for both of you.
Read more: Soft Skills for a Successful FAIR Program Launch
RiskLens can help you build a successful quantitative cyber risk management program. Talk to a RiskLens Risk Expert.