 In 2017, the shipping giant Maersk had to halt its global operations to reinstall its entire IT infrastructure-- 4,000 servers and 45,000 PCs-–after the NotPetya ransomware locked up its machines; the cost in lost business and remediation could hit $300 million.
In 2017, the shipping giant Maersk had to halt its global operations to reinstall its entire IT infrastructure-- 4,000 servers and 45,000 PCs-–after the NotPetya ransomware locked up its machines; the cost in lost business and remediation could hit $300 million.
This is one of multiple extreme cases tied to ransomware (NotPetya) that has the world on edge. These cases appear to be outliers but ransomware was the most-reported malware in the latest Verizon Data Breach Investigations Report, the authoritative yearly study.
So you're right to be worried about ransomware, but also right to step back from the headlines and take a realistic look at your organization's risk from ransomware attack. That's where FAIR (Factor Analysis of Information Risk) comes in, with a quantified risk analysis based on your data.
Here's an example of how a FAIR analyst would set up and run a scenario for the risk posed by ransomware to an organization, using the RiskLens cyber risk quantification platform. The analysis should focus on the more routine or "mundane" impacts felt by ransomware (i.e. impacts to workstations) as well as the "outlier" scenario of a NotPetya style impact.
Attend the Webinar:
Ransomware: A Recipe for Assessing Potential Financial Impact
Thursday, May 3, 2-3 PM EDT
Scoping:
For this scenario we are worried about the risk associated with an outage of our workstations due to ransomware. We will look at the more "mundane" workstation scenario as well as a broader "outlier" scenario in which shared drives are impacted.
What is our asset? Workstations and Shared Drives
Who is our Threat Actor? Cyber Criminals.
What is our effect? Loss of Availability.
Data Gathering:
Now that we know some basic information, we can look to get the right people in the room in order to ask them questions. These could be a variety of roles but mainly those who can speak authoritatively regarding the frequency of ransomware attacks against your workstations based on your historic data, the controls you have in place to prevent malware/ransomware from executing, and the process you go through to respond/fix the issue when it arises.
But what questions do you ask them? Take a look at the dialogue below, based on typical situations we encounter as RiskLens consultants:
Frequency:
Question: How often do we clean up malware/ransomware on the workstations? How many of those have spread to the company's shared drives?
Answer: We have cleaned up ransomware from at least one of our 10,000 workstations four times per year. This has happened once in the past three years
Vulnerability: Question: What percent of the time would ransomware be successful in executing? This is more like an estimate based upon your current control environment.
Answer: If ransomware happened to get past the malware protection then there is not a lot that could be done to prevent it from executing on the workstation. So the answer is "100%."
Analyst note: In this particular scenario, since the actual loss events occur on a somewhat regular basis, we did not have to estimate their vulnerability.
Loss Magnitude:
Question: What teams, number of people per team, and number of hours per person, would be involved in responding to this event, which is inclusive of investigations on how it happened and cleaning up the affected machine/shared drive in each incident?
Answer: It takes anywhere from one to four hours to re-image a workstation completed by one to two people depending on the size. Additionally, the employees affected by the ransomware would not be able to work 90% because of the lack of the workstation for a minimum of one hour. When talking about shared drives, a previous event took around two days to restore but in a worst case scenario, they could be down for up to two weeks. Depending on the job the people are tasked with, it could severely affect their productivity as well as the ability to sell our product because a lot of the processes around selling rely upon the shared drives.
In discussion with this team, it was also determined if this event were to start occurring on a more frequent basis it could pose some potential reputation damage with customers.
Results:
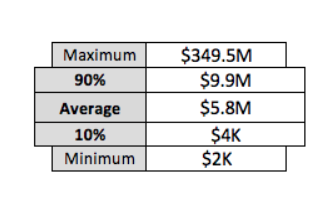
Once you have gathered all acceptable data points, the next step is to run Monte Carlo simulations in the RiskLens application. The result is a range of probable outcomes in dollar terms on an annual basis (Annualized Loss Exposure or ALE). This will allow you to quickly determine if this event is something your organization should truly be worried about or not, for instance in comparison to your risk appetite. The RiskLens analysis results also show in dollars each form of loss that goes into building the model so can easily gut check each part of the model to determine that everything makes sense and is defensible.
Since we included ransomware affecting the workstations and then spreading to the shared drive, our overall risk exposure to the scenario is below. The range of loss takes into account the best case scenario, only having to clean up one workstation and not pivoting to the shared drive, to the worst case scenario of having to clean up all the affected workstations and restoring the shared drives, where it was assumed it could take anywhere from two days to two weeks for that effort. This level of the analysis is a good opportunity to ask if the Annualized Loss Exposure across all scenarios make sense given your organization.
When we look at the results further, we can see that the RiskLens application breaks down the losses into Primary and Secondary. In this scenario, the ability to deliver our main value proposition (sell our products) poses the most potential loss from a primary perspective; from a secondary perspective the potential reputation damage is what poses the greatest threat to the organization. The important thing to keep in mind these numbers are aggregated across all of the applicable scenarios. 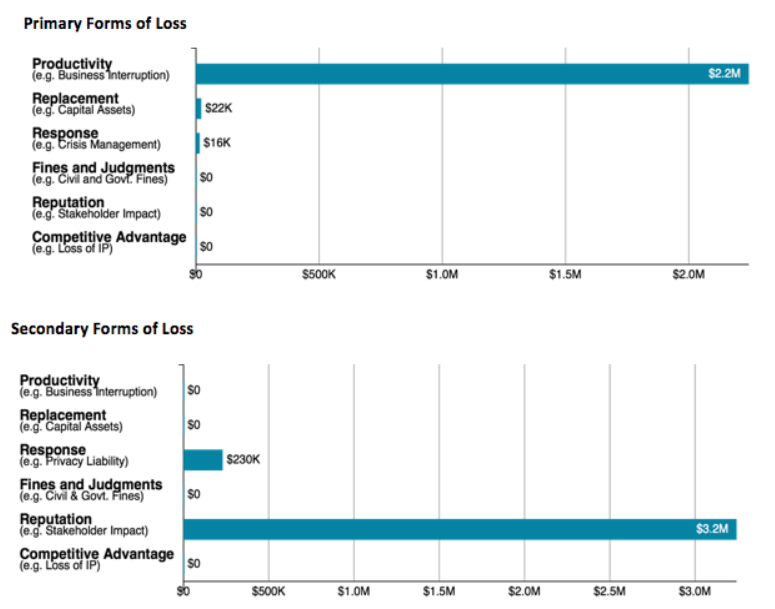 If we break down it down even further we see what the range of annualized loss would be if this event were to happen once and the costs associated with it. Since the RiskLens application allows us to consider multiple assets in one analysis it provides an opportunity to see each scenario individually. The first chart shows results if the ransomware only affected the workstations. The important thing to keep in mind is you have to take into account both the frequency of the event occurring and the magnitude of loss should it actually occur.
If we break down it down even further we see what the range of annualized loss would be if this event were to happen once and the costs associated with it. Since the RiskLens application allows us to consider multiple assets in one analysis it provides an opportunity to see each scenario individually. The first chart shows results if the ransomware only affected the workstations. The important thing to keep in mind is you have to take into account both the frequency of the event occurring and the magnitude of loss should it actually occur. 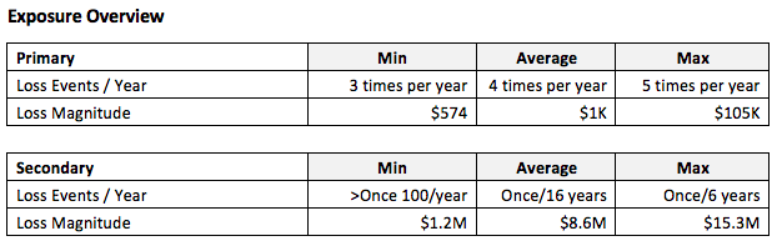
The second aspect of the analysis would take into account a NotPetya style impact - looking at what the annualized impact would be if the ransomware moved to the shared drives: 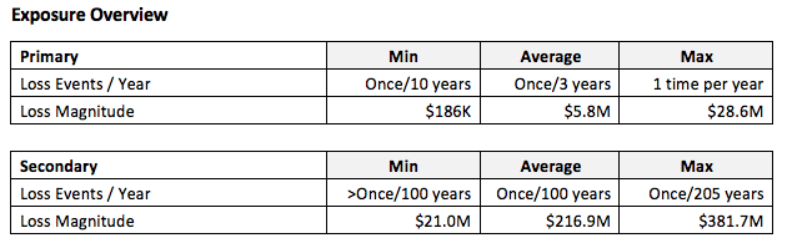
Based upon our the information received from our subject matter experts (SME's), when this analysis was reviewed with the decision makers, they agreed that the risk exposure is reasonable given their current environment. This also gave the decision makers a clear picture of their current situation as a baseline and the effect of a catastrophic, NotPetya sort of scenario.
Learn more:
The Six Types of Loss in Cyber Incidents