 Our clients tell us that the Top Risk Workshop is one of the quickest-value services RiskLens offers. It is a two- or three-day onsite workshop focussed on identification of your top risks followed by a FAIR™-based risk quantification, powered by the RiskLens platform, to quickly rank your risk scenarios for probable loss exposure. It’s a fast-paced, efficient way to launch a cyber risk quantification program for your organization.
Our clients tell us that the Top Risk Workshop is one of the quickest-value services RiskLens offers. It is a two- or three-day onsite workshop focussed on identification of your top risks followed by a FAIR™-based risk quantification, powered by the RiskLens platform, to quickly rank your risk scenarios for probable loss exposure. It’s a fast-paced, efficient way to launch a cyber risk quantification program for your organization.
Here are some of the main takeaways
1. What are my Top 20, 30, 40 risks to analyze?
During the first day of the workshop, we sit in the room with the main stakeholders and listen to what their top concerns are for the organization. Typically, they are IT-related and we begin to develop risk scenarios that can be analyzed around these concerns. Often, these are broad worries like “the cloud” that need to be turned into a true FAIR scenario by defining the threat, the asset and the effect. We call this normalization.
Example: “The Cloud”
Normalized: Analyze the risk associated with an External Malicious actor breaching PII data within our cloud service Vendor.
We do this for about 20 - 40 scenarios until we have a list that represents those most probable scenarios, to then run through the rapid analysis function in the RiskLens Platform.
About RiskLens Rapid Analysis
This capability of the RiskLens platform allows risk analysts to:
- Ingest data from the organization on frequency and magnitude of cyber events, enhanced by industry-specific data curated by RiskLens and made available on the RiskLens platform through handy Data Helpers and Loss Tables
- Run a quantitative risk analysis of a list of scenarios in 15 minutes to determine the probable financial loss exposure each one poses
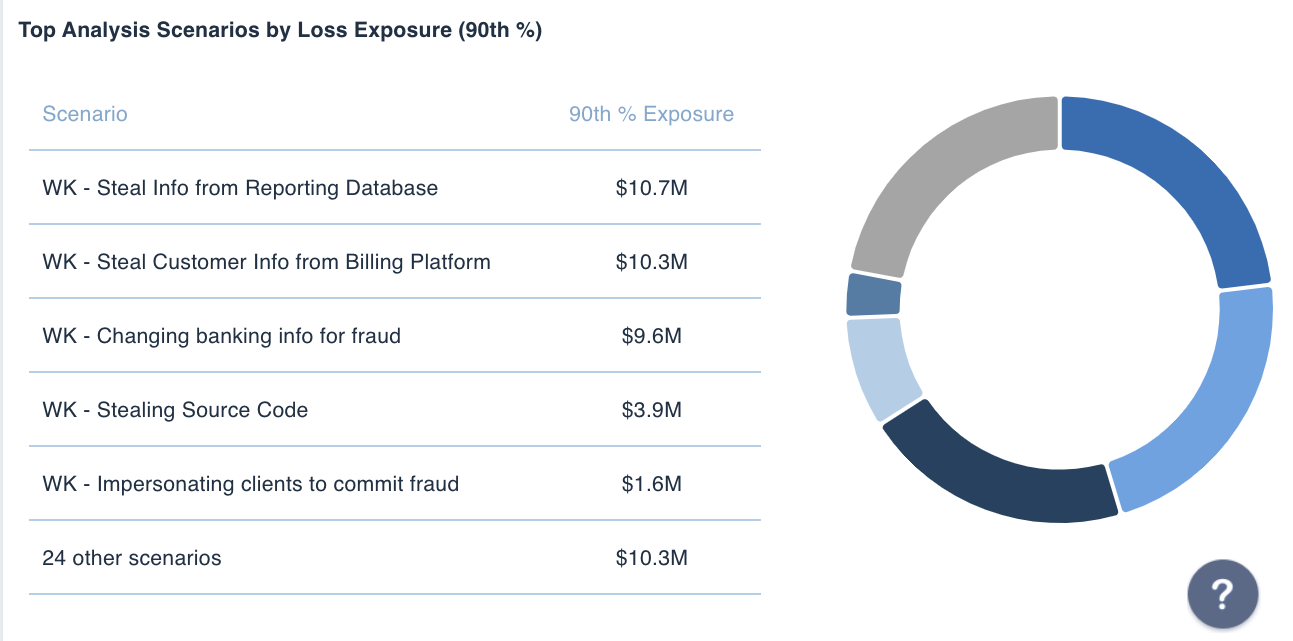
2. Analyze risks for magnitude: Where is my highest loss exposure?
Among the chosen scenarios, RiskLens reporting helps you to quickly assess and understand where your highest exposure lies. What threats should you really be concerned with – for instance, Insiders or External Malicious Actors? Should you be concerned more about the cloud or on-premise databases containing PII? What about effects – should your organization focus more on protecting data or keeping your systems online? From rapid risk analysis, we will give you decision support for those questions in quantitative terms.
3. Analyze risks for frequency: What loss events are occurring most frequently?
We hear this called death ‘by a thousand cuts’ and every organization has several. There may be normal processes that run – legacy systems, customer emails, any manual process – where you are experiencing outages or breaches every day, once a week, whatever it may be. Every time these happen, it may not be a long outage or a huge breach, but these little events add up and could be costing your organization a lot of money.
4. Ranking your risks: How much in dollars could I potentially lose?
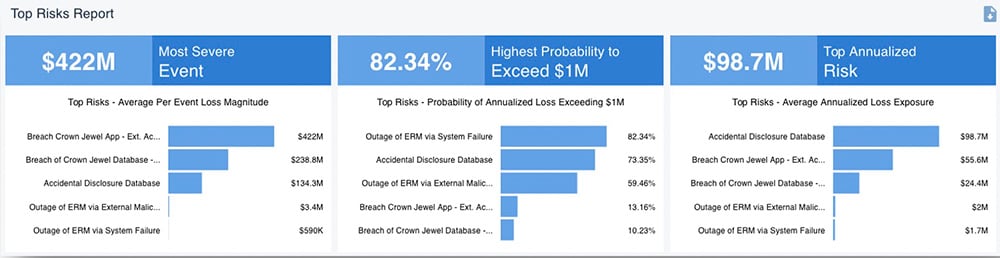
Once we analyze all scenarios for magnitude and frequency, we come out with a set of quantitative results and can rank the scenarios by probable loss. We do not use a high/medium/low scale - we are able to quantify this future loss as annualized loss exposure.
Additionally, we are not just producing single-dollar values but a range of probable outcomes and through several lenses (for instance, most costly single events, most likely to exceed a set threshold or most costly on an annual basis. RiskLens provides a true decision support capability through our platform. It is a great starting point to help us prioritize security efforts. It’s perception versus reality. We have our moved from our perceived top risks to the reality of risks that we should be concerned about.
A RiskLens Top-5 Risks Report
5. What are the next steps?
The RiskLens Professional Services team will coach you on next steps based on our experiences with other clients and peers in your industry. We may suggest you do a deeper dive on the RiskLens platform into your top five risks to get a more precise understanding of how much risk you face by gathering more data from the business and relevant stakeholders. Maybe one scenario really stands out and that is where you should start to focus your security efforts. Additionally, if you have certain objectives you’d like to achieve after this – reporting to the board, validating investments/projects, etc. we can help you achieve those.
Most importantly, we can set you up with an ongoing cyber risk quantification program with the RiskLens platform so you can make FAIR-based analysis an ongoing part of your risk and security operation.