Many RiskLens clients take their first step into cyber risk quantification with a Top Risk Workshop, using the rapid analysis function in the RiskLens platform to quickly identify a short list of high-risk scenarios for deeper quantified analysis. Here’s the Top Risks experience for one major tech company.
The Challenge
Technology companies are constantly competing to bring the most innovative products to market. With each technological advancement comes additional risk exposure that the organizations must be able to effectively identify, measure, and prioritize. But risk management often takes a backseat to product development, seen as an offramp in the way of speed to market.
The risk management team at a major tech company was looking for a way to break through that mindset and win a seat at the decision-making table. One point on their side: The company was subject to reporting to the SEC, following the agency’s 2018 guidelines on disclosure of cyber risk in financial terms.
However, the qualitative heat maps the team used to guesstimate risk didn’t give them the ability to:
- Identify, measure, and prioritize the risks that are most important to business operations
- Evaluate the top risk scenarios including insight into highest-risk assets and threat communities
- Effectively communicate the posture of the cyber risk program to executive management in order to adhere to the “timely collection and evaluation of information potentially subject to required disclosure” as required by SEC guidance
The Solution
The team turned to the RiskLens platform that enables quantitative cyber risk analysis with the Factor Analysis of Information Risk (FAIR™) model to help address the above requirements in a more meaningful way.
1. Identify, measure, and prioritize the risks that are most important to business operations
In order to effectively quantify risk, FAIR requires consistently defining scenarios based on assets at risk, threats and loss effects. The organization leveraged this approach by identifying the most critical assets, the most likely threat actors, and the most probable and/or impactful ways in which the loss would materialize.
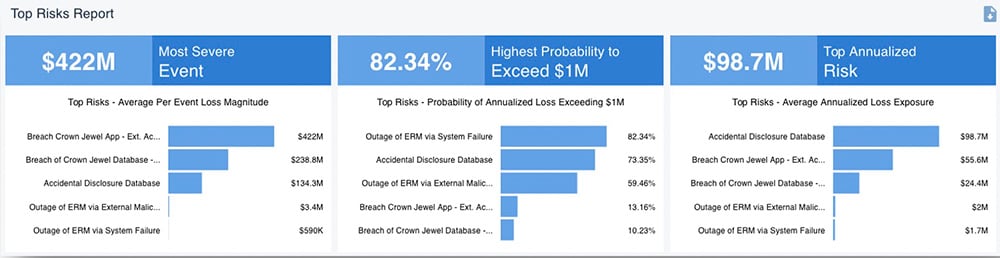
Once the most probable and impactful scenarios were identified, the list was quickly prioritized based on loss exposure using the rapid analysis function in the RiskLens platform. This exercise was completed over the course of a two-day Top Risk Workshop led by experienced consultants from the RiskLens Professional Services team.
Top Risks Report
2. Evaluation of top risk scenarios including insight into highest-risk assets and threats
With a target list in hand, the team could run detailed analyses of individual risks based on more extensive data gathering within the organization and through curated industry data provided by RiskLens. The goal was to get a more accurate picture of the risk and identify the key drivers of loss exposure.
Detailed Risk Analysis

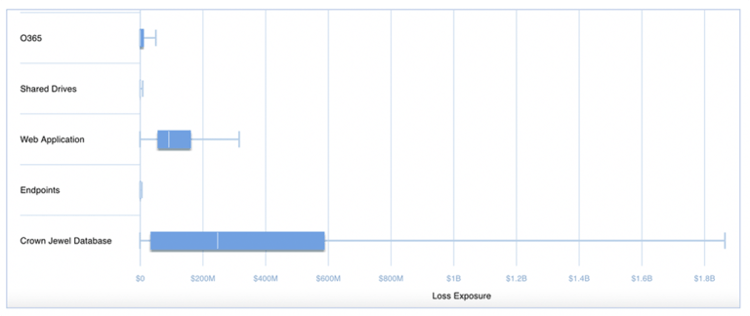
The team was also able to drill down into the top risks aggregate annualized exposure and view the highest-risk threat communities and assets.
Aggregate Loss Exposure by Threat Community 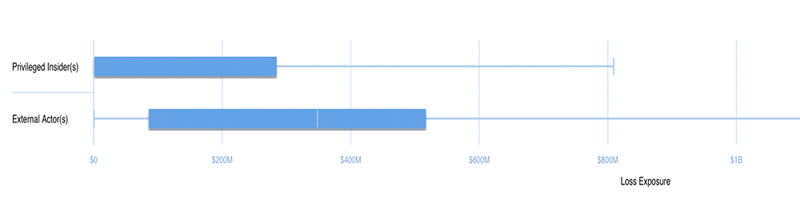
Aggregate Loss Exposure by Asset
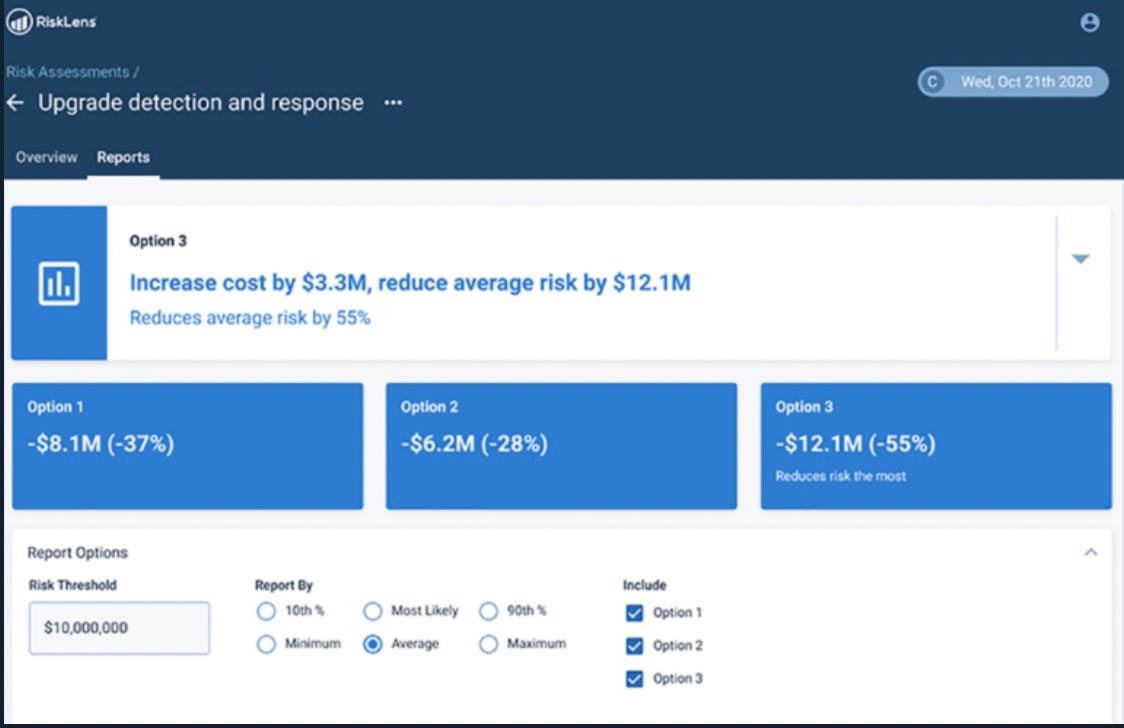
3. Compare risk mitigations for effectiveness in risk reduction
With the Risk Treatment Analysis capability of the RiskLens platform, the team could apply those risk insights to plan changes in controls or security processes and game out the effect on risk reduction in dollars to find the most cost-effective alternative.
4. Effective communication of cyber risk management strategy to executive management
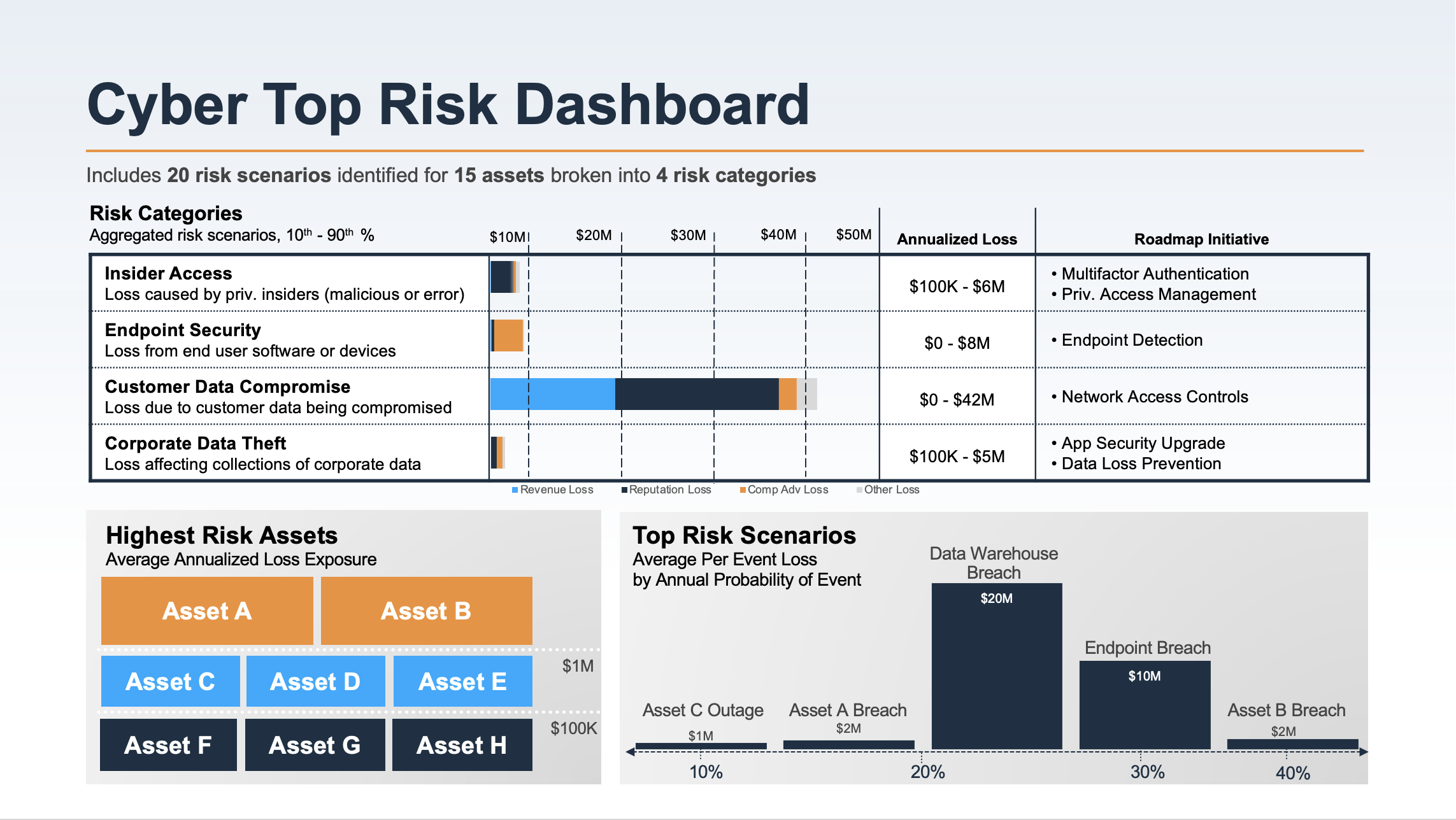
With the help of the RiskLens platform powered by the FAIR model, the organization was able to report on the top risks to executive management and the board in the language they best understand – dollars and cents. They could also present cost/benefit analysis pointing the way to risk reduction. Going forward, they could maintain a dashboard for executive reporting on the risk themes of most importance to the organization, updated by APIs pulling from the latest analyses on the RiskLens platform.
Dashboard generated via API from the RiskLens platform
Results and Key Benefits
With the Top Risk analysis in hand and experience with FAIR quantitative cyber risk analysis, the risk team had found their credibility builder, demonstrating it could communicate the impact of cyber risk in the financial terms that the board, senior management ,and regulators could understand. With a clear view of Top Risks, the organization could then leverage further FAIR analyses to support decision-making on
- Evaluation of control adequacy
- Prioritization of mitigation efforts
- Determination of cyber insurance needs
- Justification of additional security investments and controls -- particularly covering new products the organization plans to roll out, going forward.
See how the RiskLens platform and Professional Services can bring the power of cyber risk quantification to your organization. Schedule a demo.