 Replacing an EMR or EHR system is an expensive proposition, but dissatisfaction with functionality or interoperability often drives healthcare payers and providers to scout the market. With ransomware and other cyber threats so prevalent, security should be high on the list of features in your comparison shopping.
Replacing an EMR or EHR system is an expensive proposition, but dissatisfaction with functionality or interoperability often drives healthcare payers and providers to scout the market. With ransomware and other cyber threats so prevalent, security should be high on the list of features in your comparison shopping.
The RiskLens Cybersecurity Prioritization and Justification solution for healthcare payers was built to run thorough risk assessments based on cyber risk quantification to identify an organization’s top risks and compare the risk reduction effects of security controls and processes. It’s also a solid starting point to understand your security needs in shopping for an electronic medical records system. Here’s a five-step walkthrough of how that works, using the RiskLens platform:
Rebecca Merritt is Sr. Manager, Professional Services, with RiskLens
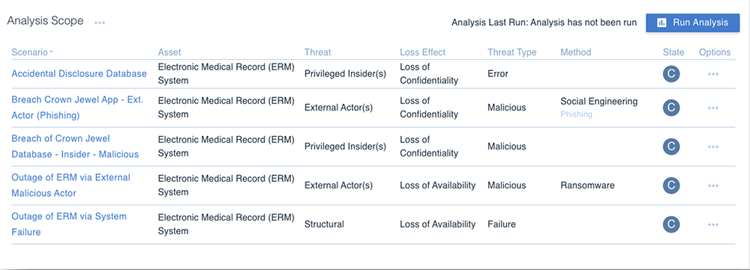
Step 1 – Scope Cyber Risk Scenarios for an EMR System
Scope out relevant scenarios. What is your current security concern with the system you have in place. Is it the availability of the system or data? Are you worried about the confidentiality of the data or the integrity of the data within the system?
This is where you should scope in the things that matter to the organization and represent in risk scenarios that demonstrate the current state loss exposure the organization may face with the system currently in use.
Analysts Tip: When scoping always be sure to include all elements of a FAIR scenario – asset, threat, effect.
Training: Learn FAIR quantitative cyber and technology risk analysis from RiskLens Academy
Step 2 – Rapid Risk Assessment
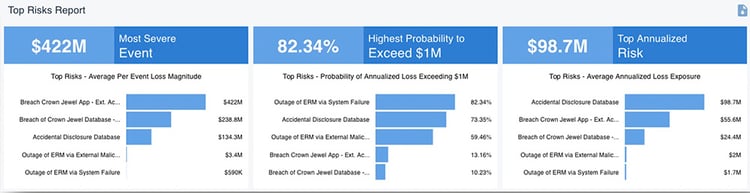
When you have many scenarios to assess, it is best to start with a Rapid Risk Assessment – meaning you focus on quick assessment with the use of the "Triage" mode in the RiskLens platform and ready-to-use Data Helpers in your instance of the RiskLens platform.
The goal of Rapid Risk Assessment is to quickly measure and prioritize the list of scenarios you have identified. QA should be performed during this stage to determine which scenarios, if any, need to be further refined to drive precision into our analyses. Analysts may choose to engage the business on the scenarios that boil to the top to validate the data inputs and refine when necessary.
Step 3 – Refine Data, Run Detailed Risk Assessments
Step 3 involves the potential for a deeper dive into the scenarios assessed above. This is where you may choose to further refine some of the data helpers or data inputs you’ve originally used. Some common areas to gain more precision may be to further home in on the record count input within a confidentiality scenario or the outage timeframe expected within an availability scenario. Then take a more detailed look at critical risk scenarios with a Top Risk Assessment.
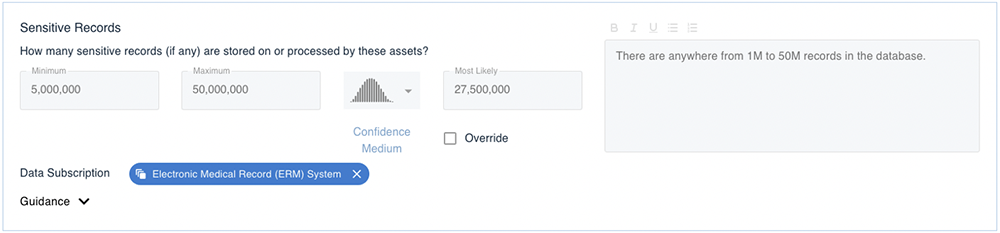
Rapid Risk Assessment input – wider range – accurate with less precision
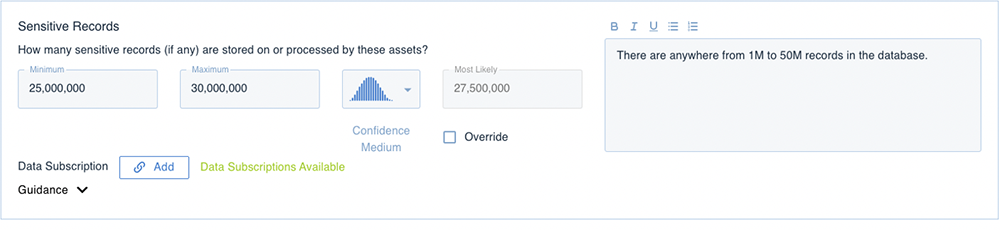
Detailed Assessment – refined data inputs – accurate with additional level of precision – based on conversation with SME
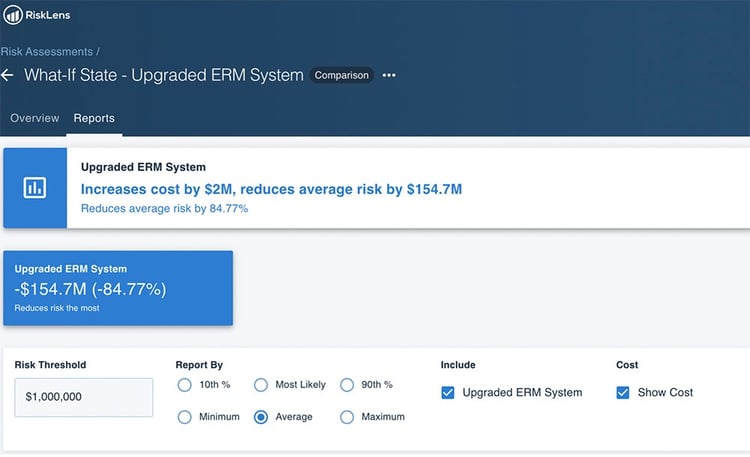
Step 4 – Measure Change in Loss Exposure
This is where the future state investment comes into play. Some critical questions to ask those with knowledge of a proposed EMR investment:
- How would it reduce our risk of a breach – from an internal and external standpoint?
- Does the system have controls in place to reduce downtimes or system failures?
- Are there improvements to ensure the integrity of the data within the new system?
- Is there more automation in the new system that would reduce manual error?
- What is the cost of the investment?
From here we can start to map these answers back to our current state and note where we would expect a reduction in risk (quantified in dollars) given the new system and controls that could be implemented.
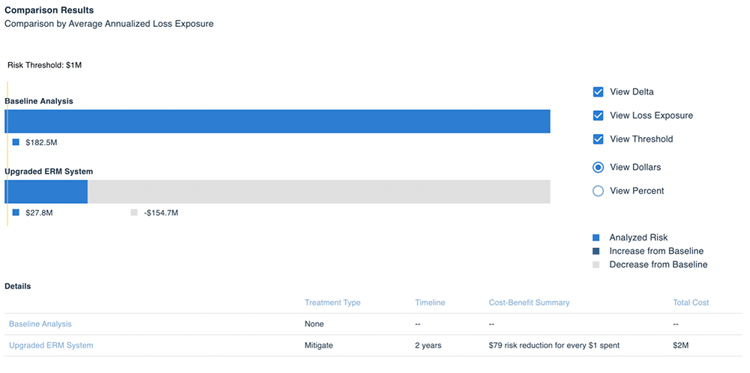
Step 5 - Report to the Decision-Makers
Report out results and work with the business to drive decisions. This is where the rubber meets the road – where you can really drive change and optimize business spend. Ensure that the reporting reaches the right stakeholders to drive conversation within the organization.
Related:
