Starting in October, 2020, with their fiscal year 2021 budgets, federal agencies are required to report on their IT investments to OMB following Technology Business Management (TBM), the standardized framework for aligning IT spending with organizational objectives.
TBM is all about proving value: demonstrating a business case, performing ROI analysis, showing application total cost of ownership, measuring cost performance or justifying budget. But when it comes to IT spending for cybersecurity, federal agencies are about to run into a roadblock. The typical cybersecurity program can’t show in financial terms its effectiveness in reducing cyber risk. An investigation by the Government Accountability Office (GAO) in 2019 of cyber risk management at 23 agencies found widespread failure and confusion, basically for lack of direction on how to assess risk and the value of cybersecurity.Ted Stettinius is Federal Practice Leader for RiskLens
But here’s the good news. FAIR™ (Factor Analysis of Information Risk), the standard for quantifying cyber risk in financial terms (and the model that’s operationalized by the RiskLens platform), enables the cost-effective, mission-aligned, risk-based approach to cybersecurity that TBM and other federal mandates demand. Even more relevant, FAIR is aligned with NIST, whose Cybersecurity Framework (NIST CSF) is the foundation of federal cybersecurity.
About FAIR FAIR provides a standard risk taxonomy as well as a model for understanding, analyzing and quantifying information risk in financial terms. Unlike traditional risk assessment frameworks that focus their output on qualitative and highly subjective color charts or numerical weighted scales, FAIR builds a foundation for developing a bottom-line approach to cyber risk management. With FAIR, organizations can communicate about risk in the non-technical language of dollars and cents, and prioritize risk mitigation projects based on ROI.
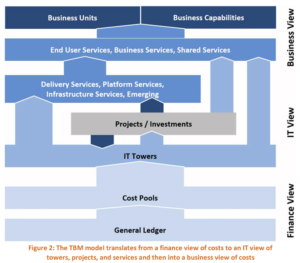
FAIR and TBM Similar in spirit to FAIR, the TBM model guides users on a path that starts with financial considerations, moves through IT assets and applications to business services and ultimately to organizational mission. The Cyber Security & Incident Response section of the TBM documentation (see page 25) ) directs users to “determine associated risk to ensure the organization has the appropriate defense and responses to each incident” but doesn’t define how to determine or quantify that risk. Thus, FAIR, as the standard for quantifying cybersecurity risk is, in effect, a necessary component for implementing TBM in the information security space – and to fulfill the spirit of federal directives.
Federal Recognition for FAIR
The NIST Cyber Security Framework (CSF), mandated for government agencies by Executive Order in May, 2017 includes FAIR as an “Informative Resource” for meeting the framework’s standards for Risk Assessment and Risk Management Strategy. The CSF builds on NIST SP 800-53, the security controls guidelines for federal agencies to comply with the Federal Information Security Act (FISMA). Agencies are scored annually in the FITARA process on how well they meet FISMA requirements.
Learn more: NIST's Advice: Integrate Cyber Risk with Enterprise Risk Using FAIR™ (FAIR Institute)
 RiskLens for Agency-wide FAIR Adoption
RiskLens for Agency-wide FAIR Adoption
To implement, scale and report at the agency-wide level TBM requires, you need more support than the FAIR model alone provides. RiskLens has standardized the best practices for enterprise-level adoption of FAIR into a suite of SaaS solutions based on the RiskLens-FAIR Enterprise Model™ (RF-EM™). RiskLens is the number one provider to the Fortune 1000 for expert solutions for quantitative risk management. Contact us to learn more.
FAIR Is Already in Use in the Federal Government
Department of Energy CISO Emery Csulak and NASA Chief Cyber Risk Officer Cody Scott discussed their implementations of FAIR on a panel at this year’s RSA Conference ( watch the video) . The DOE is using FAIR to assess risk on another federal mandate, cloud migration, and more broadly, committed in its energy sector cybersecurity plan to “use risk-based methods to make decisions and prioritize activities to support the risk management responsibilities of energy owners and operators.”