One thing we learn from Factor Analysis of Information Risk (that’s the FAIR™ model that powers the RiskLens cyber risk quantification platform) is to take a disciplined approach to our thinking and language about risk. A good example: risk analysis vs. risk assessment, two terms commonly thrown around as interchangeable -- but there is an important difference.
Key differences between risk analysis and risk assessment (in FAIR practice):
- A risk analysis quantifies the risk (or loss exposure) of a single loss event, which can be analyzed as a risk scenario like this:
“Analyze the risk associated with a malicious privileged insider impacting the confidentiality of the PII in the Crown Jewel Database, via mis-use of their access.”
- A risk assessment is the larger process that includes running analyses, identifying the options to remediate the risk, and reporting to stakeholders. A risk assessment might also encompass multiple risk analyses covering, for instance, the loss exposure for a business unit.
Learn FAIR quantitative risk analysis from the RiskLens Academy
The good news here: The RiskLens platform walks you through all the steps of risk analysis and risk assessment in the risk management process. Let’s take them one at a time:
1. Rapid Risk Assessment
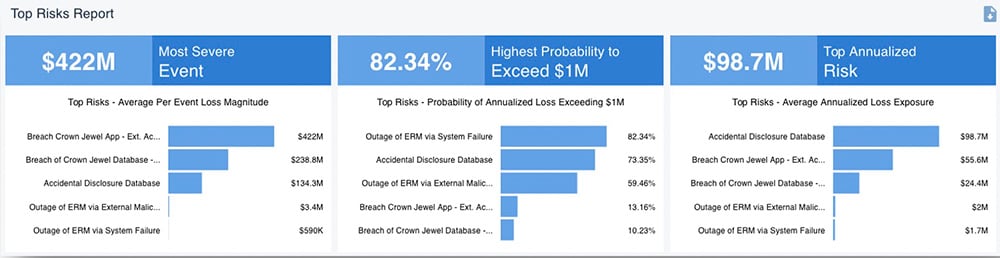
The Rapid Risk Assessment capability of the RiskLens platform allows you to quickly assess many risk scenarios around a common theme (e.g., insider threats), an asset (crown jewel database), a business unit or the entire enterprise, and prioritize them for their probable loss exposure in dollars. To speed the process, the analysis runs on pre-packaged data from RiskLens Data Helpers and loss tables.
2. Detailed Analysis of Top Risks
After Rapid Risk Assessment, organizations typically run a detailed Top Risk Assessment on each of the top risk scenarios. This is an opportunity to gather data more intensively from subject matter experts, including the relevant history of cyber incidents, the probable threat actors, the costs associated with incident response or secondary effects such as lawsuits, and the controls in place. Again, the workshop format of the RiskLens platform shows the way. With the data in place, analysts run a Monte Carlo simulation to generate a range of probable outcomes for the loss event, as in this example:

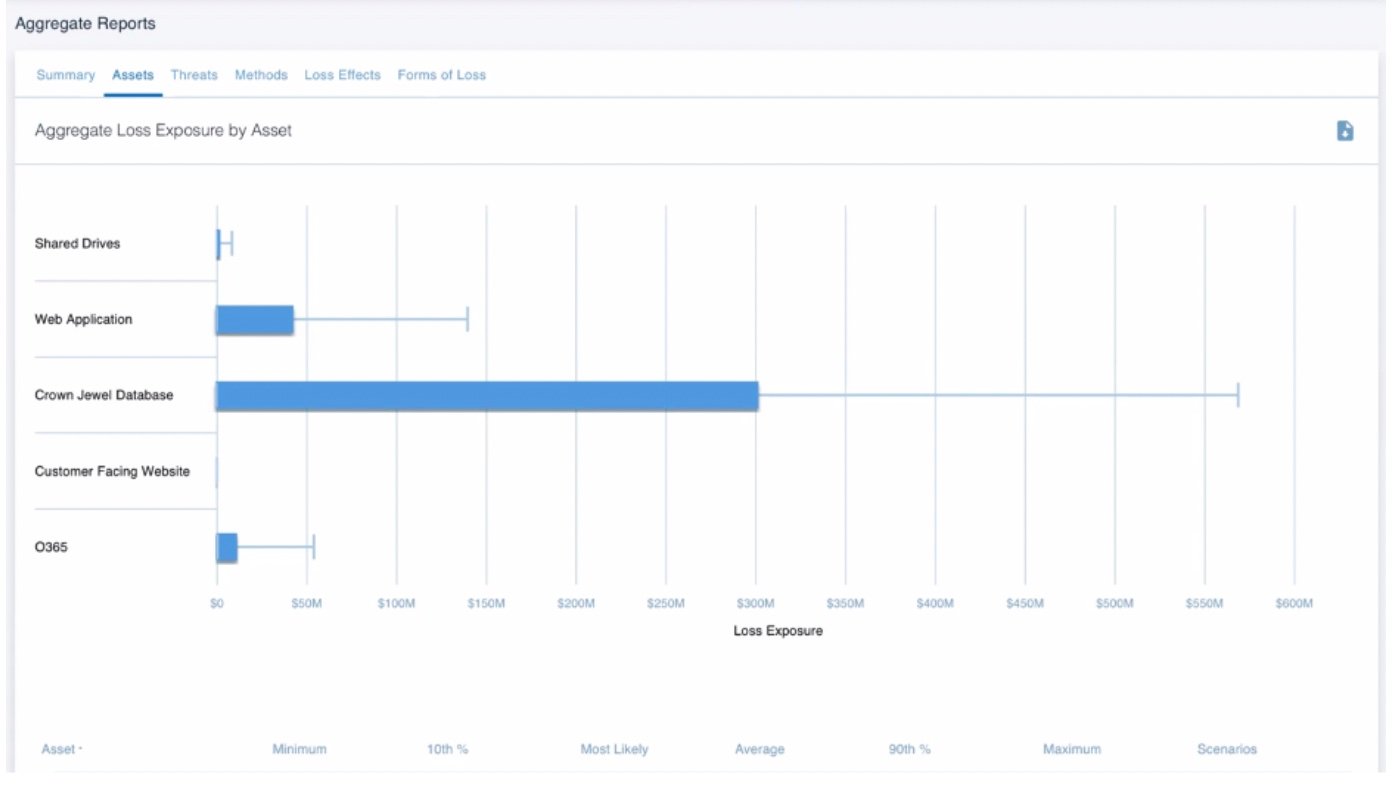
3. Aggregating Risk Scenarios into a Risk Assessment
With a detailed picture of risk scenarios, analysts can now aggregate scenarios into risk assessments for deep insights into the loss exposure of the organization. For instance, a CISO might see which threat communities or asset types pose the greatest probable risks across a business unit or the enterprise.
4. Making Cyber Risk Analysis Actionable with Risk Treatment Analysis
A rule of thumb in cyber risk management: Don’t present decision makers with a risk without risk treatment options for them to choose among. The Risk Treatment Analysis (or Comparison Assessment) capability of the RiskLens platform compares controls or process changes for their effect on the factors of the risk under analysis and probable risk reduction of each. Add in the cost of the mitigations and the analysis shows the return on investment.
5. Reporting Results: Risk Analysis or Risk Assessment?
Cybersecurity risk reporting can be divided into two types, tactical and strategic, depending on business needs. Tactical reporting might cover day-to-day issues such as audit findings, policy exceptions or control variances, and would be best handled by a quick risk analysis. Strategic reporting to the C-suite, Board or Enterprise Risk Management might be best served by risk assessments to answer big-picture questions such as “How much material risk do we have and what are we doing about it?” Either way, the FAIR standard gives risk managers solid basis for prioritizing risks and justifying risk management tactics and strategy.
Learn more:
How to Conduct a Detailed Analysis of a Top Cyber Risk with RiskLens
Bring quantitative cyber and technology risk assessment to your organization – talk to a RiskLens risk expert.