Before getting started on cyber risk quantification, let's be clear on what we mean by measuring risk. On a weekly basis, we observe risk registers from organizations that are an absolute mess. They are flooded with entries that are inconsistently defined. If we don’t define risk consiste
ntly, then how we analyze it can’t be any better.
How to Unscramble Your Risk Register with FAIR [Video]
Let’s look at a non cyber-related risk analysis to explain: Car Insurance
An automobile is an asset.
Can we measure the frequency and magnitude of an automobile?
Nope. Note: we see risk registers populated with assets like “cloud”, “mobile devices”, etc.
A teenage driver is a “threat”.
Can we measure the frequency and magnitude of a teenage driver? Nope.
Note: we see risk registers populated with threats like “malicious insider”, “nation-state”.
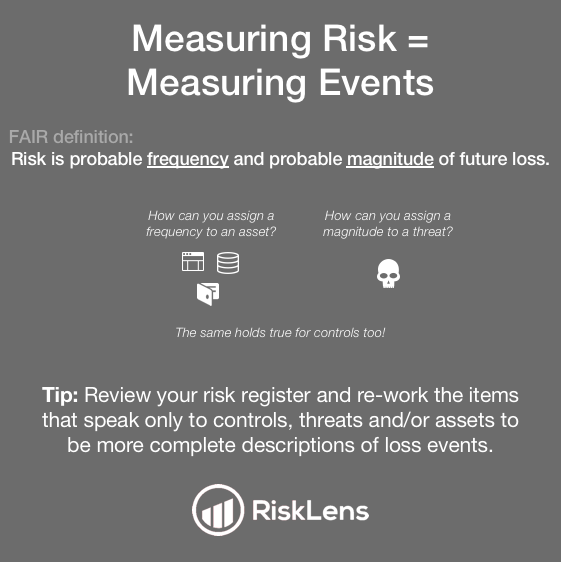 What can we measure?… An event!
What can we measure?… An event!
When we assess risk (which is the frequency and magnitude of future loss) we can only assign those values to events.
Based on the information above we can surmise the risk (or substitute the word "event") we are actually trying to measure is “How much risk is associated with automobile accidents caused by teenage drivers”.
Learn More
If you want to learn more about properly defining risk I would like to point to our online training at the RiskLens Academy. If you are new to FAIR - check out the FAIR Analysis Fundamentals course. If you’ve been doing FAIR analysis for some time but understand the importance of scoping, check out our Analyst Learning Path for more advanced training to raise your game. For an ongoing education in cyber risk analytics, join 3,000 of your peers as a member of the FAIR Institute.