 In a phased rollout by 2025, the 300,000 contractors and subcontractors for the Defense Department must comply with the new Cybersecurity Maturity Model Certification (CMMC) process, intended to tighten controls on handling unclassified information, if they hope to continue doing business with the DoD. Government or third-party auditors will certify compliance, including meeting the CMMC framework’s guidelines on risk assessment and risk management.
In a phased rollout by 2025, the 300,000 contractors and subcontractors for the Defense Department must comply with the new Cybersecurity Maturity Model Certification (CMMC) process, intended to tighten controls on handling unclassified information, if they hope to continue doing business with the DoD. Government or third-party auditors will certify compliance, including meeting the CMMC framework’s guidelines on risk assessment and risk management.
CMMC is essentially a list of best practices and a maturity model -- and practitioners of FAIR™ (Factor Analysis of Information Risk), the international standard for cyber risk quantification that’s the basis of the RiskLens platform and services, will recognize it as another opportunity to meet and exceed requirements and turn a compliance exercise into a true effort at risk reduction.
Ted Stettinius is Federal Practice Leader for RiskLens
Here are some of the important facts to know about FAIR and the CMMC:
NIST Recommends FAIR for Risk Assessment and Risk Management
CMMC is largely based on the National Institute of Standards and Technology publication NIST SP 800-171, “Protecting Controlled Unclassified Information (CUI) in Nonfederal Systems and Organizations” that lists recommended types of cybersecurity controls and processes. Several of these cover risk, such as :
3.11.1 “Periodically assess the risk to organizational operations (including mission, functions, image, or reputation), organizational assets, and individuals, resulting from the operation of organizational systems and the associated processing, storage, or transmission of CUI.”
3.12.1 “Periodically assess the security controls in organizational systems to determine if the controls are effective in their application.”
800-171 itself does not recommend specific means to assess risk or determine controls effectiveness, leaving it to the businesses to determine what best fits their business needs.
However, NIST has cited FAIR as an informative reference in meeting the CSF ID.RA-1 controls which NIST has mapped to the above referenced 800-171 controls.
The bottom line: Defense contractors looking for a defensible standard for a federal audit can confidently turn to FAIR for the required risk components.
Learn more:
NIST Recommends FAIR for Integrating Cybersecurity with Enterprise Risk Management
Meet the New NIST Standard for Integrating Cybersecurity into ERM with RiskLens Risk Assessment
FAIR Can Also Help on the Maturity Model Side of CMMC
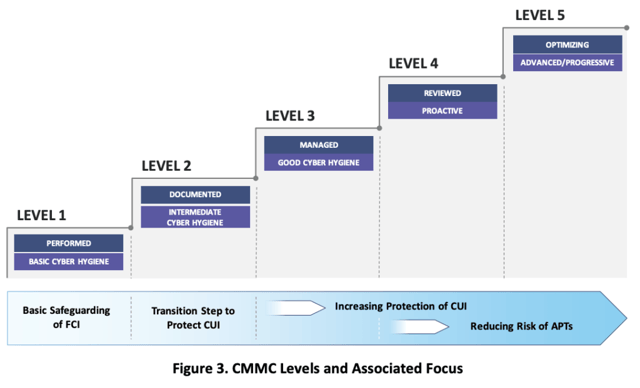
The CMMC requires that contractors show proficiency on five progressing levels of maturity over time to maintain their access to contracting opportunities. Risk management is one of the categories, for instance:
Level 3
“Periodically perform risk assessments to identify and prioritize risks according to the defined risk categories, risk sources, and risk measurement criteria”
Level 5
“Analyze the effectiveness of security solutions at least annually to address anticipated risk to the system and the organization based on current and accumulated threat intelligence.”
Again, the CMMC doesn’t specify how to “prioritize risks” and “analyze effectiveness” but, as NIST has recognized, the clearest way to understand and communicate on cyber risk assessment and management is by quantifying risk in financial terms, so that, for instance, risks can be prioritized for their probable impact in dollar loss and controls can be analyzed for their effectiveness in reducing loss exposure in dollar terms – two deliverables from FAIR analysis on the RiskLens platform, presented in reporting that would be easily understood by auditors.
Learn more:
RiskLens Rapid Risk Assessment
RiskLens Risk Treatment Analysis
FAIR Analysis = CMMC Compliance with Benefits
With FAIR analysis on the RiskLens platform, defense contractors can document compliance with the risk assessment and risk management requirements of the CMMC following a standard that’s already widely accepted in business and government – not just to follow the letter of the rules but to target compliance where it will bring the best return on security investments to protect data. Learn more on how RiskLens supports defense contractors – get in touch with us.