The Impact of Increased Regulation
Regulations aim to safeguard information technology and computer systems with the purpose of obliging organizations to protect their systems and information from cyberattacks.
Importance of Risk Quantification
Regulatory expectations have significantly increased along with the pace and scale of cyber threats, requiring organizations to develop processes to continuously quantify and manage their cyber risk exposure in defensible ways.Increased Frequency and Size of Fines
Both Boards and Business Executives have subsequently increased their focus, attention on cybersecurity initiatives, as they face a dramatic increase in potential regulatory fines and actions.Industries Most Heavily Impacted
As a response to the growth of cyber threats, regulatory bodies have issued guidelines and standards to ensure necessary cybersecurity processes and controls are in place across the healthcare, financial services, and government sector to minimize the impact of an attack.Utilizing Quantification for Cyber Risk Management Programs
RiskLens’ cyber risk quantification is the most defensible and consistent methodology to combat risk and prioritize consumer interest.
Board & Regulatory Reporting & Communication
Cyber risk quantification keeps the board up-to-date on new and emerging critical risks. It also helps communicate and respond to inquiries and concerns thorough a defensible analysis at the most material events.Overall Risk Appetite
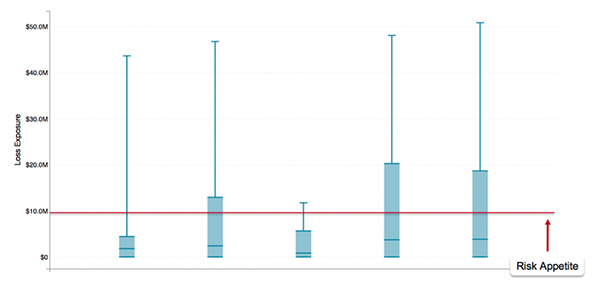
Teams must identify relevant loss events, define thresholds for “unacceptable” loss exposure, and validate risk appetite using sample quantitative risk scenarios.Integration with Maturity Frameworks
Most companies in regulated industries leverage frameworks such as NIST-CSF and HITRUST with their risk management programs to make them more standardized and defensible. The FAIR™ standard integrates with and complements maturity frameworks to further improve programs and decision making.Identify Relevant Loss Events
Risk appetite may not represent a single value for cyber events. Rather, risk appetite may be defined differently for each event. We recommend our customers start the process by first focusing on the types of loss that are most relevant to their organization.Define Unacceptable Loss Exposure Levels
It is important to establish leading questions to help drive the discussion around risk appetite. Rather than directly asking for risk appetite, develop a list of proxy questions to help drive the discussion such as “what is our current cyber insurance coverage?” and “What does materiality look like from a financial reporting perspective?”Validate Risk Appetite with Sample Quantitative Risk Scenarios
Once an initial risk appetite value has been established, it’s important to benchmark this figure against previously quantified FAIR risk analyses and obtain buy-in from key stakeholders.Overcome Challenges in Adopting FAIR™ and Quantitative Risk Management
Discover how RiskLens helped a Fortune 500 financial firm work through the corporate-culture challenges that many organizations face in stepping up to FAIR and a quantitative risk management approach to cybersecurity.
Watch the Webinar