 I recently led a webinar The Solar Winds Hack: A FAIR Perspective, and at the end an audience member asked this question about cyber risk quantified analysis:
I recently led a webinar The Solar Winds Hack: A FAIR Perspective, and at the end an audience member asked this question about cyber risk quantified analysis:
“How do we handle threat actors who are constantly evolving their tactics and techniques?”
It’s a question I’ve heard before as a RiskLens risk consultant, as well as another question, coming from a similar place:
“How can I practically create risk scenarios for analysis when I have over 100 assets?”
Essentially, they are both asking how to conduct risk analyses when you can’t get your arms around two of the three main elements of a risk scenario: Threat Actor → Asset → Impact.
The answer to both questions starts here: Understand which assets are most critical to your business. These might be anything from customer-facing web applications to databases that house sensitive information that, if they were disrupted or locked down by ransomware, for instance, would do serious harm to your business.
Learn quantitative cyber risk analysis. Get trained on the FAIR standard.
In order to identify those critical assets, you have to get out of the mindset of cybersecurity risk, learn the business and how it makes money. Relating that back to assets is what some of my clients have called the “crown jewel exercise.”
As you go through this research, keep the factors of FAIR™ (Factor Analysis of Information Risk) in mind so you’re asking questions that feed your analysis. Questions like, “What’s the type of loss for this asset (confidentiality, integrity, availability)?”, “What controls are in place to prevent unauthorized access?” or “What type of data is stored in the asset?”
So, it may be obvious how that would lead to prioritizing the list of 100 assets down to a manageable few. But what about those ever-evolving and emerging threat actors?
Now, it’s true that threat actor TTP (tactics, techniques and procedures) evolve over time. Like any of us, they grow in their jobs – in fact, they are often forced to innovate their methods. Attacks have signatures to them, and threat actors will pivot from attack to attack so they can’t be identified and profiled. But mostly, they are tweaking their existing techniques to get around your security controls.
Most importantly, threat actors are known for targeting specific types of assets and types of organizations -- that doesn’t change, most of the time it’s only their techniques that do. So, starting with your high-value assets gives you a starting point for analysis on threat actors, as well.
Next stop to help with analyzing threats is your Security Operations and Threat Intelligence groups. A lot of organizations know the threats that are targeting them, but they don’t have an open flow of communication with the risk management team. Risk analysts should be in the habit of going to the SOC or Threat Intel and sharing the development of risk scenarios to confirm what threat actors would make sense to include.
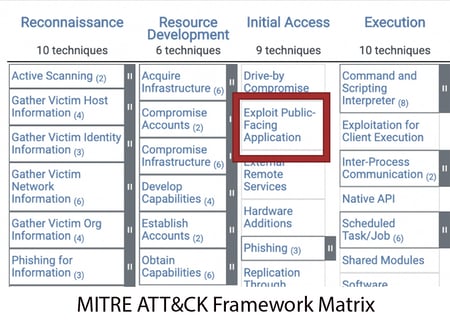 Once you’ve identified the assets, prioritized them and identified your threats with the help of your SOC departments, I recommend next going to the MITRE Att&ck framework, an extensive resource for identifying the actors who tend to go after your sort of organization or have key skills to attack your defined assets. The framework breaks down their likely techniques and suggest mitigations to thwart them. (I wrote a blog post on integrating MITRE Att&ck with FAIR analysis.)
Once you’ve identified the assets, prioritized them and identified your threats with the help of your SOC departments, I recommend next going to the MITRE Att&ck framework, an extensive resource for identifying the actors who tend to go after your sort of organization or have key skills to attack your defined assets. The framework breaks down their likely techniques and suggest mitigations to thwart them. (I wrote a blog post on integrating MITRE Att&ck with FAIR analysis.)
So, to sum up, know your assets, know the likely threat actors, sharpen your FAIR risk scenarios, and, while threat actors may keep evolving, so will you.
RiskLens helps CISOs prioritize and justify cybersecurity investments based on quantitative cyber risk analysis. Contact us to learn more.