 “Cyber risk management programs must be able to effectively prioritize an organization’s cyber risk concerns and choose cost-effective solutions. Both require the ability to measure cyber risk well.”
“Cyber risk management programs must be able to effectively prioritize an organization’s cyber risk concerns and choose cost-effective solutions. Both require the ability to measure cyber risk well.”
--Jack Jones, RiskLens Chief Risk Scientist, creator of the FAIR™ standard for cyber risk quantification
As Jack writes in the Buyer’s Guide to Cyber Risk Quantification, general agreement in the cybersecurity world is that quantitative risk assessment is necessary to measure cyber risk well – the disagreement is over what counts as cyber risk quantification.
Some call “quantification” rating risks 1-5 based on the subjective opinions of the risk team. Others use numeric rating systems for vulnerability scans or “maturity” in complying with frameworks such as NIST CSF as a quantitative risk assessment template.
While those may be useful for technical decisions for the cybersecurity team, at RiskLens, we define cyber risk quantification as a means to prioritize and justify business decisions in financial terms, based on Factor Analysis of Information Risk (FAIR).
Definition: Cyber Risk Quantification with FAIR
“Loss event probability is expressed as a percentage (e.g., 10% probability of occurrence in the next 12 months) and magnitude is expressed as a loss of monetary value (e.g., $1.5M). These values can be combined to express risk as an annualized amount (e.g., $150,000).”
--Buyer’s Guide to Cyber Risk Quantification
Quantitative Risk Assessment Example
Assess the amount of risk associated with an external actor breaching sensitive information held on workstation shared storage, putting the data at risk of exfiltration.
Analysis results from the RiskLens platform established baseline risk (or loss exposure) with data from the company on loss event frequency and magnitude, then compared probable risk reduction from adding controls to support a business decision (in this case, to implement drive-level controls).
Get the details in this case study:
Finance Company Assesses Risk of Data Breach from Shared Storage
Learn FAIR quantitative risk assessment with the RiskLens Academy
6 Advantages of Quantitative Risk Assessment for Cybersecurity
Estimating cyber risk loss exposure in financial terms unlocks many advantages for security and risk teams seeking better communication about cyber risk and prioritization of security projects. Here are some of the key benefits:
1. Establish a common language of cyber risk for the security and risk teams.
Not simply a risk quantification standard, FAIR is a logical and consistent way to understand and measure risk. Once the teams are trained, it eliminates misunderstandings and “religious disputes” over what should be considered high, medium or low risks.
2. Communicate cyber risk to the business in the financial terms the business understands.
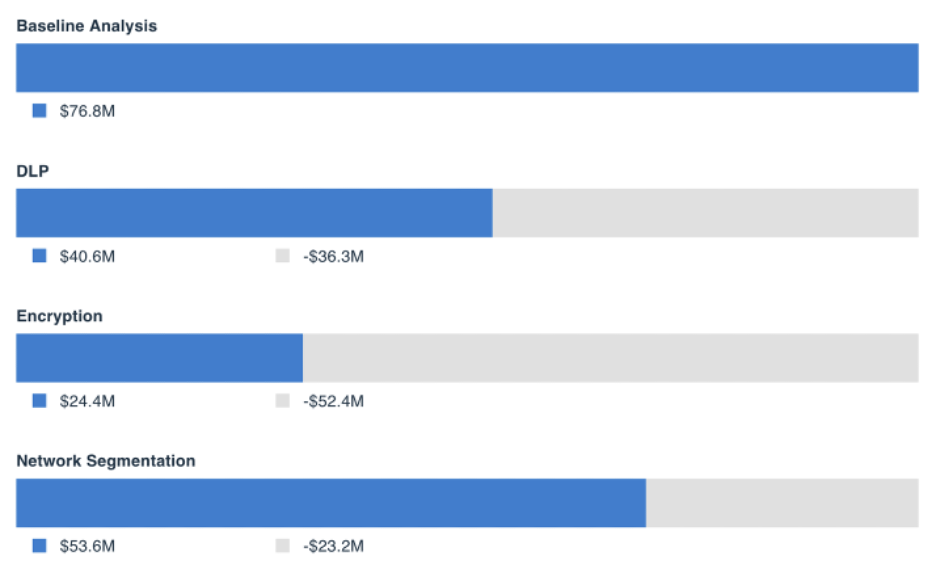
As in the quantitative risk assessment example above, presenting to senior staff or the board a finding that encryption will reduce probable loss exposure by $5.8 million, or $5.80 for every dollar spent, is a credible statement that’s on par with cost/benefit analysis that business leaders expect to see in a budget request. It’s also defensible: If questioned, FAIR risk analysts can document all the data sources.
Read More:
Making It Easier and Faster to Optimize Your Cybersecurity Budget
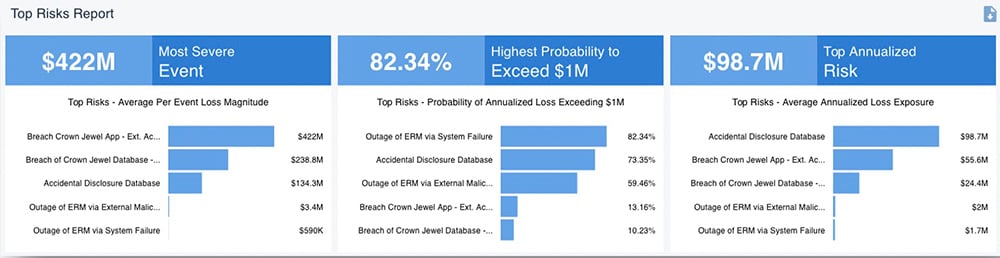
3. Compare and aggregate risks to understand top risks and overall loss exposure.
Without quantification in financial terms, comparing and prioritizing risks isn’t practically possible – which risks on the red side of a heat map are redder than the other reds? As an example, the RiskLens platform’s Rapid Risk Assessment capability can sort an organization’s risks into a prioritized list in minutes based on probable loss exposure. Similarly, aggregating risks for a picture of total loss exposure for the organization or subsets (such as risk from nation-state threat actors) requires apples-to-apples measurement among those risks. Once aggregated risk assessments are set up, analysts can report on trends over time to show progress in risk reduction.
4. Triage everyday risks and clean up the risk register.
Risk and security teams are frequently on the receiving end of audit findings or vague requests from the business to assess risks that really aren’t (like “the cloud”) – and many of these get dumped into the risk register with no way to prioritize them. With FAIR analysis, risk managers can render GRC entries into quantifiable risk scenarios to quickly prioritize (or even reject) audit findings.
Read more:
How to Utilize a Risk Register in Cybersecurity
Reacting to IT Audit Findings? Get Ahead of Them with Cyber Risk Quantification!
5. Set a risk appetite.
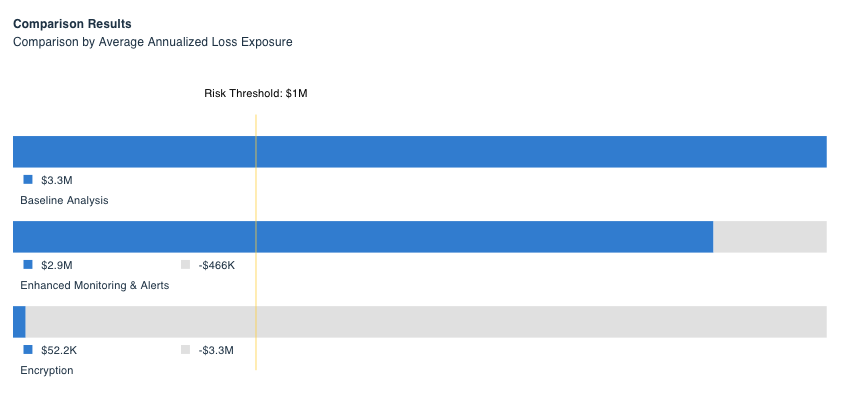
It’s a crucial piece of guidance that senior management or the board can give to the cyber side of the business, but setting a risk appetite is difficult when risk can’t be quantified. With quantified risk assessments, cybersecurity teams can identify the loss events that are most relevant, run analyses, then define a risk threshold for unacceptable loss exposure ($1 million in example below).
Read More:
How to Set a Cyber Risk Appetite with RiskLens
6. Meet compliance frameworks in a cost-effective way and satisfy the regulators.
Many businesses base their cybersecurity programs on NIST, ISO, CIS or other frameworks that are essentially lists of controls and best practices. They help organizations understand broadly areas of control deficiencies; with quantitative risk assessments, organizations can understand how to prioritize among the recommendations based on return on investment for risk reduction. Organizations that are regulated by the SEC, FINRA or other agencies can use quantification to defensibly meet standards for disclosing material risks.
Webinar:
Combining NIST CSF and FAIR to Drive Better Cyber Risk Decisions
Learn FAIR quantitative risk assessment with the RiskLens Academy